PAM360Privileged Access Management
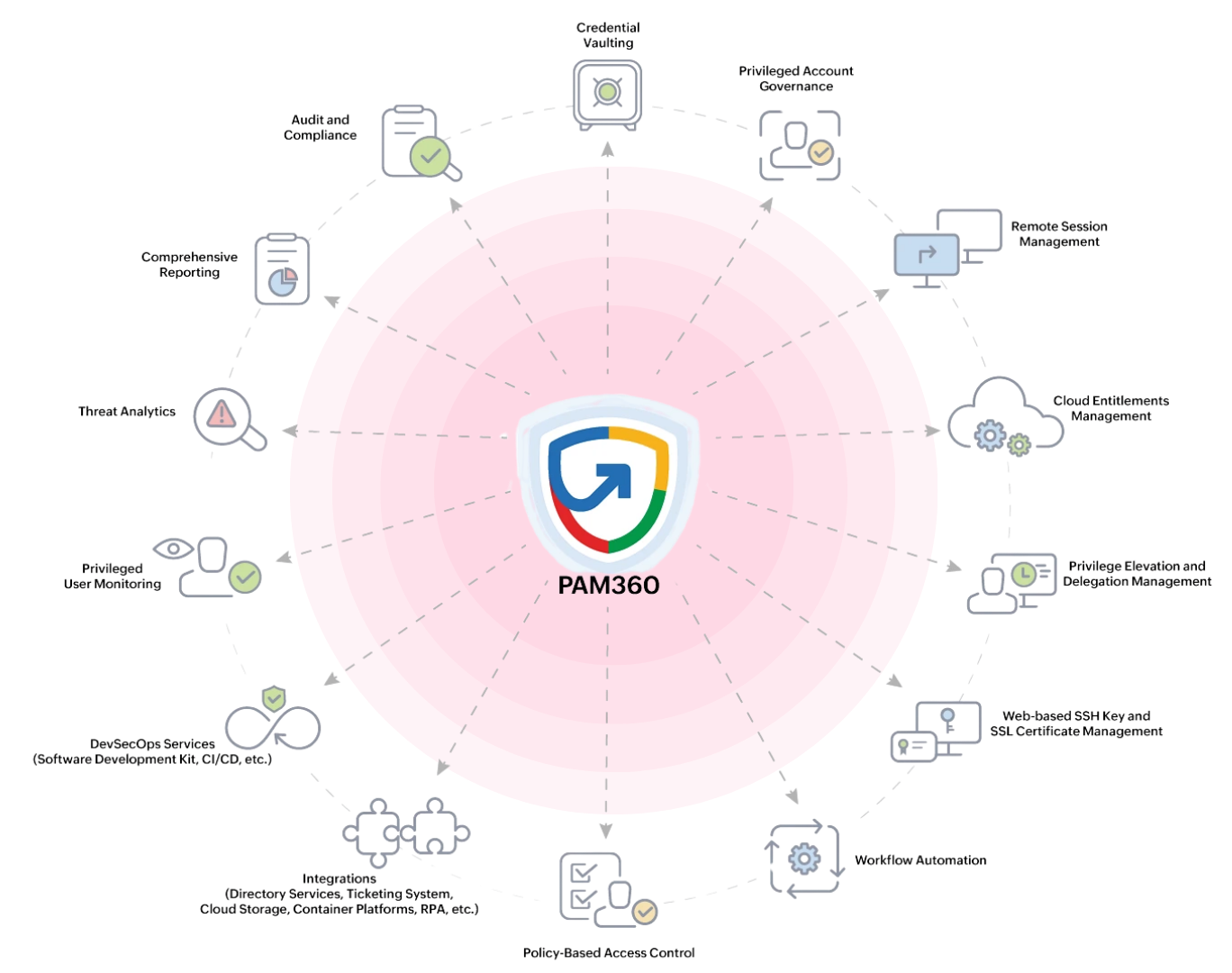
Protect your organization's most sensitive systems and credentials with ManageEngine PAM360 – Privileged Access Management. Our PAM solution helps organizations control, monitor, and secure privileged accounts that have elevated access to critical infrastructure, servers, databases, and network devices. Privileged accounts are the primary target for cyber attackers. PAM360 enables secure credential vaulting, session monitoring, and access governance to prevent unauthorized access and significantly reduce the risk of insider threats and credential theft.
What Is Privileged Access Management?
Privileged Access Management (PAM) is a cybersecurity discipline focused on securing, controlling, and auditing privileged accounts that hold elevated permissions within an IT environment. Using ManageEngine PAM360, organizations can securely vault sensitive credentials, enforce granular access policies, record privileged sessions, and prevent unauthorized administrative access. By implementing PAM, businesses dramatically reduce the risk of credential theft, insider threats, and privilege misuse—which account for the majority of major security breaches worldwide.
What Do We Secure?
We secure and manage privileged access across your entire IT infrastructure.
Privileged Account Management
Discover, onboard, and manage all administrator and service accounts across your infrastructure in a centralized, secure vault.
Learn moreCredential Vaulting
Encrypt and securely store passwords, SSH keys, API tokens, and sensitive credentials with strict access controls and audit trails.
Learn morePrivileged Session Monitoring
Record and monitor every administrative session in real time with full video replay capabilities for accountability and forensics.
Learn moreAccess Control Policies
Implement role-based access controls with granular just-in-time permissions to enforce the principle of least privilege.
Learn morePassword Rotation
Automatically rotate and update privileged credentials on a schedule, eliminating stale passwords and reducing breach risk.
Learn moreRemote Access Security
Provide secure, audited remote access to critical systems for administrators without exposing direct credentials.
Learn moreAudit & Compliance Tracking
Maintain detailed, tamper-proof audit logs of all privileged access activities to support regulatory compliance investigations.
Learn moreInsider Threat Protection
Detect behavioral anomalies in privileged user activity and receive immediate alerts on suspicious or unauthorized actions.
Learn moreOur Implementation Process
We follow a structured approach to deploy and optimize your PAM solution effectively.
Privileged Asset Discovery
We conduct a thorough discovery of all privileged accounts, credentials, and sensitive systems across your IT environment.
PAM Deployment & Configuration
ManageEngine PAM360 is installed and securely configured with hardened settings aligned to your organization's security policies.
Access Policy Setup
Granular role-based access controls and just-in-time privilege policies are defined and enforced across all privileged accounts.
Credential Vault Integration
All privileged credentials are securely onboarded and stored with encrypted vaulting and automated password management.
Monitoring & Session Recording
Privileged sessions are monitored in real time with full recording, behavioral analytics, and anomaly detection active.
Reporting & Compliance
Comprehensive audit reports, access logs, and compliance dashboards are generated to support security and regulatory reviews.
Why Choose Us?
Certified Security Experts
Our team brings deep expertise in privileged access security with hands-on experience across complex enterprise environments.
Secure Credential Vaulting
Protect all critical credentials with AES-256 encryption, strict access policies, and automated password lifecycle management.
Complete Session Visibility
Every privileged session is recorded and monitored, providing full accountability and enabling rapid forensic investigations.
Automated Password Management
Eliminate stale password risks with intelligent, policy-driven automatic credential rotation across all privileged accounts.
Insider Threat Protection
Behavioral analytics and real-time session monitoring detect and alert on suspicious privileged user activity instantly.
Compliance Ready
Built-in support for ISO 27001, PCI-DSS, GDPR, HIPAA, and SOC 2 compliance frameworks with audit-ready reporting.

Virendra Gawande
Information Security Officer
Key Benefits
Why Our Privileged Access Management Delivers Real Security Value
Centralized Credential Control
Securely manage and store all privileged credentials in a centralized, encrypted vault with granular access policies.
Reduced Insider Threat Risk
Monitor privileged user activity continuously and detect misuse of administrative accounts before damage occurs.
Strong Access Governance
Enforce strict, role-based access policies and just-in-time privilege elevation to apply the principle of least privilege.
Complete Audit Visibility
Tamper-proof session recordings and detailed access logs support security investigations and regulatory compliance audits.
Automated Credential Security
Automatic password rotation eliminates stale credentials and significantly reduces the risk of credential-based attacks.
Enhanced Security Posture
Protect critical infrastructure, sensitive data, and business systems from unauthorized privileged access and credential theft.
Ready to Secure Your
Digital Infrastructure?
Let's Discuss Your Security Needs
Reach out to our experts and get actionable insights to protect your business.
Request a Security Assessment
We'll get back to you within 24 hours.
