
OWASP Top 10: The Most Critical Web Security Risks Every Business Must Know in 2026
Cybersecurity threats do not discriminate by company size. Whether you run a two-person startup or a multinational enterprise, if your business has a web application, you are a target. The Open Web Application Security Project (OWASP) has been cataloguing the most dangerous web application vulnerabilities since 2003, and the 2025 edition the 8th installment of the Top 10 is the most comprehensive analysis yet, drawing on over 175,000 CVE records and 589 Common Weakness Enumerations.
The average cost of a data breach in 2025 exceeded $4.8 million. Most breaches trace back to one or more vulnerabilities on this list. The OWASP Top 10 is not a technical document it is a business risk brief.
In 2025, two brand-new categories entered the list: Software Supply Chain Failures — reflecting the explosive growth of third-party ecosystem attacks and Mishandling of Exceptional Conditions, which addresses how poor error handling creates real attack opportunities. Server-Side Request Forgery (SSRF) has been rolled into the Broken Access Control category, and Security Misconfiguration has surged to the #2 spot. Let us walk through every risk, what it means for your business, and how to defend against it.
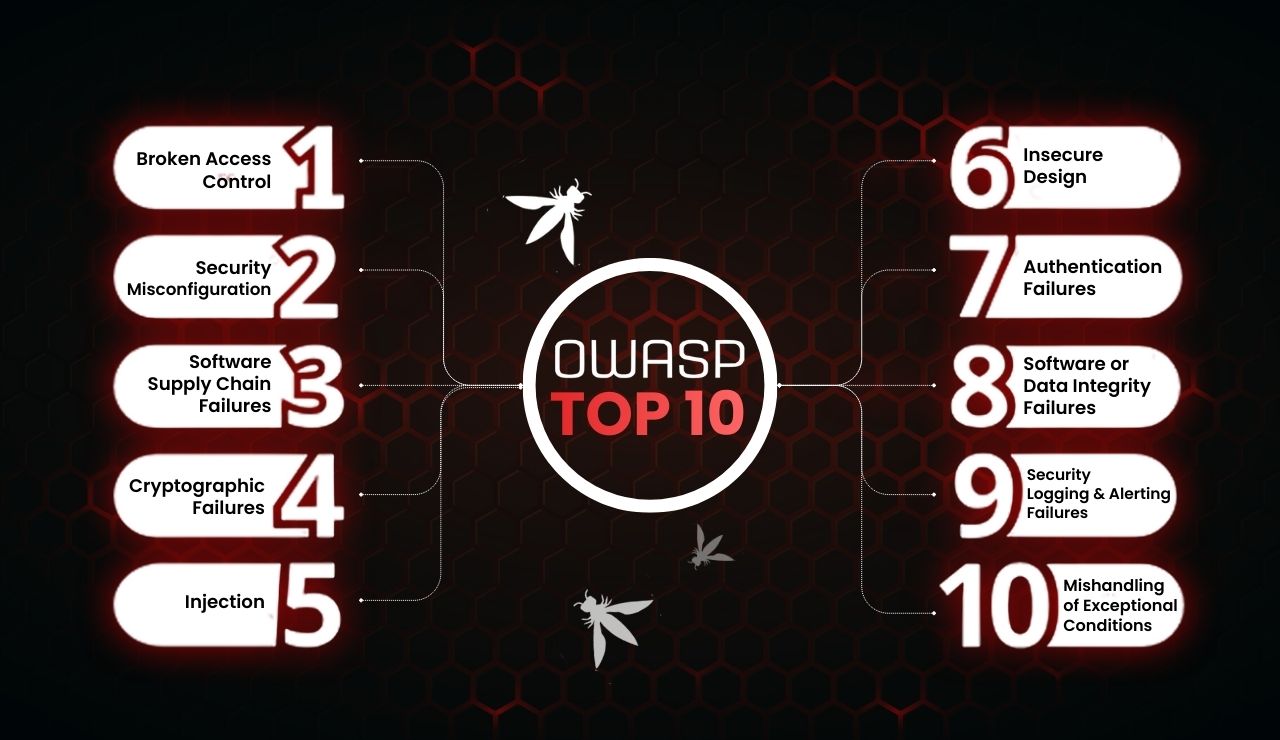
OWASP Top 10 (2025) – The Latest Security Risks
Here are the latest OWASP Top 10 vulnerabilities for 2025.
1. Broken Access Control
Broken Access Control sits at the top of the OWASP list for the second edition running and for good reason. An average of 3.73% of all tested applications contain at least one of 40 associated CWEs. This category covers any scenario where an application fails to properly enforce what authenticated users are allowed to do.
In practice, this looks like a customer being able to view another customer's orders by changing a number in the URL (Insecure Direct Object Reference), a regular user accessing an admin dashboard, an API returning data it should restrict, or a cloud server being tricked into making requests to internal services on an attacker's behalf (Server-Side Request Forgery, now included here). These are not rare edge cases they are among the most commonly discovered vulnerabilities in real-world applications.
⚠ Business Impact
Unauthorised access to customer data, financial records, or admin functions. Potential GDPR/data protection fines. Reputational damage if a breach is disclosed. High severity: can lead to full system compromise.
✓ How to Defend
Implement deny-by-default server-side access controls. Validate every request, not just the first. Use ownership checks on every data resource. Log and alert on access control failures. Conduct regular penetration tests focused on privilege escalation.
2. Security Misconfiguration
Security Misconfiguration has made the biggest jump of any category from position #5 in 2021 to #2 in 2025. It now affects approximately 3% of all tested applications, with over 719,000 individual CWE instances recorded across 16 CWEs. This surge reflects the increasing complexity of modern applications: the more your system's behaviour depends on configuration files, cloud settings, and environment variables, the larger the misconfiguration attack surface becomes.
Common examples your team should watch for: cloud storage buckets left publicly accessible, default admin credentials unchanged on deployment, overly verbose error messages that expose database schemas or internal paths to end users, unnecessary HTTP methods or services left enabled, missing security headers (Content Security Policy, HSTS, X-Frame-Options), and XML External Entity (XXE) injection vulnerabilities caused by insecure XML parser defaults.
⚠ Business Impact
Publicly exposed sensitive data, unauthorised system access via default credentials, data theft from misconfigured cloud storage. Increasingly the entry point for ransomware campaigns targeting businesses without proper cloud security posture management.
✓ How to Defend
Build automated configuration checks into your deployment pipeline. Follow hardening guides for every technology in use. Remove default accounts and sample apps pre-production. Conduct quarterly configuration audits. Use Cloud Security Posture Management (CSPM) tools for cloud environments.
3. Software Supply Chain Failures
The most significant new addition of the 2025 edition. This category expands well beyond the previous "Vulnerable and Outdated Components" to encompass the entire software supply chain: third-party dependencies, package registries, build systems, CI/CD pipelines, and distribution infrastructure. It was the top concern voted by the security community in OWASP's annual survey — and it has the highest average exploit and impact scores of all categories in the CVE data.
The threat model here is direct: a single malicious open-source package, a compromised developer account on npm or PyPI, or a tampered build artifact can propagate backdoors to thousands of organisations simultaneously. The 2024 XZ Utils backdoor where a sophisticated attacker spent months as a trusted maintainer before introducing a backdoor exemplified just how advanced and patient these supply chain adversaries have become. Most businesses have little visibility into the full dependency trees their applications rely on.
⚠ Business Impact
Backdoors silently embedded in production applications. Complete system compromise without any direct attack on your own infrastructure. High risk for businesses using open-source libraries — which is virtually every modern application. Often results in data exfiltration before detection.
✓ How to Defend
Maintain a Software Bill of Materials (SBOM) for all applications. Pin and verify dependency versions in lockfiles. Integrate dependency scanning (e.g. Dependabot, Snyk) into every pull request. Treat your CI/CD pipeline as a critical security boundary. Implement code signing for build artifacts.
4. Cryptographic Failures
Previously titled "Sensitive Data Exposure," this category was deliberately renamed to Cryptographic Failures to focus attention on the root cause. It drops two positions but remains a critical risk, affecting an average of 3.80% of applications tested across 32 mapped CWEs. The slight drop reflects improving industry adoption of TLS and modern password hashing — but cryptographic failures remain deeply consequential when they occur.
Common failures include storing passwords using MD5 or SHA-1 (broken algorithms), transmitting sensitive data without encryption, hardcoding API keys and cryptographic secrets in source code repositories, using predictable random number generators for security tokens, and failing to properly validate TLS certificates. Every one of these mistakes can lead directly to credential theft, impersonation, and data compromise at scale
⚠ Business Impact
Mass credential compromise if password databases are cracked. Regulatory penalties under GDPR, HIPAA, PCI-DSS for failure to protect sensitive data. Loss of customer trust. Exposed API keys can lead to cloud resource abuse and surprise billing in the tens of thousands.
✓ How to Defend
Use Argon2, bcrypt, or scrypt for password hashing — never MD5 or SHA-1. Enforce TLS 1.2+ everywhere. Manage secrets using a dedicated vault (HashiCorp Vault, AWS Secrets Manager). Scan repositories for accidentally committed credentials. Never build custom cryptography.
5. Injection
Injection has been on every edition of the OWASP Top 10 since the list began and remains among the most dangerous vulnerability classes despite dropping two spots. It has the greatest number of CVEs of any category — 38 associated CWEs. The slight ranking drop is a sign of industry maturation: widespread adoption of parameterized queries, ORMs, and modern templating engines has reduced classic SQL injection prevalence. However, new injection surfaces in GraphQL APIs, NoSQL databases, and AI prompt interfaces continue to emerge.
Injection attacks work by inserting malicious code or commands into data inputs that are then executed by the application. SQL Injection can dump or destroy entire databases. Cross-Site Scripting (XSS) can steal user sessions, redirect users to phishing pages, or silently mine cryptocurrency in visitors' browsers. OS command injection can grant an attacker full server control. These are not theoretical — they remain the bread and butter of opportunistic cybercriminals worldwide.
⚠ Business Impact
Complete database exfiltration. Account takeover via XSS session theft. Full server compromise via command injection. Direct financial impact. One of the most exploited vulnerability classes in criminal toolkits available on the dark web.
✓ How to Defend
Mandate parameterized queries and prepared statements — no exceptions. Apply server-side input validation with allowlists. Use context-aware output encoding for web output. Implement a strict Content Security Policy to mitigate XSS. Apply least-privilege to all database accounts.
6. Insecure Design
Insecure Design, introduced in 2021, slides two positions but remains critical. Its slight ranking drop is partly good news: OWASP notes that the industry has made noticeable improvements in threat modeling and secure design practice since the category's debut. But this does not mean the problem is solved — design-level flaws are among the costliest to fix because they require architectural changes, not just code patches.
An application can be perfectly coded, use no deprecated libraries, and still be fundamentally insecure if its design is flawed. Classic examples include password reset flows that rely on security questions rather than verified channels, financial systems with no transaction rate limiting that can be abused for fraud, multi-tenant platforms that share database rows across customers without logical separation, or authentication flows that assume a browser's behavior rather than verifying it server-side.
⚠ Business Impact
Design flaws cannot be patched — they require expensive architectural refactoring. They are often discovered late in development or after deployment, dramatically increasing remediation cost. Business logic flaws can be silently exploited for months without triggering security alerts.
✓ How to Defend
Integrate threat modeling in the design phase — before a line of code is written. Use established secure design patterns and reference architectures. Establish security requirements alongside functional requirements. Bring security specialists into architecture reviews. Conduct design-focused red team exercises.
7. Authentication Failures
Renamed from "Identification and Authentication Failures" to more accurately reflect the 36 CWEs in this category, Authentication Failures holds steady at #7. The slight reduction in prevalence data is likely attributable to the growing adoption of standardised authentication frameworks — OAuth 2.0, OpenID Connect, passkeys, and SSO providers. However, custom authentication implementations remain a significant risk, and credential stuffing attacks continue to grow in volume as leaked credential databases expand.
This category covers weak or predictable passwords that can be brute-forced, the absence of multi-factor authentication on sensitive accounts, insecure session tokens that can be stolen or forged, sessions that are not properly invalidated after logout, and "remember me" implementations that expose persistent credentials. Credential stuffing — where attackers use email/password pairs leaked from other breaches — is now an industrial-scale threat that most businesses underestimate.
⚠ Business Impact
Account takeover leading to data theft, financial fraud, or ransomware deployment. Regulatory breach notification obligations if customer accounts are compromised. Significant reputational damage in the event of a public breach disclosure. High risk for businesses with B2C portals.
✓ How to Defend
Enforce MFA on all privileged and user-facing accounts. Implement account lockout, CAPTCHA, and anomaly detection for repeated login failures. Use long, randomly generated session tokens with Secure and HttpOnly flags. Integrate with established identity providers rather than building custom auth. Monitor for credential stuffing patterns.
8. Software or Data Integrity Failures
This category focuses on failures to verify the integrity of software and data at the artifact level — operating below the supply chain concerns of A03, addressing how individual components and data flows are trusted without verification. The most dangerous vulnerability in this category is insecure deserialization, which can directly lead to Remote Code Execution — the worst possible outcome in web application security.
Other examples include loading JavaScript libraries from external CDNs without Subresource Integrity (SRI) hash checks (meaning a CDN compromise could inject malicious code into your site), auto-update mechanisms that apply patches without verifying digital signatures, and CI/CD pipelines that pull from package registries without integrity verification. For businesses that serve JavaScript to millions of users, a single compromised CDN dependency can turn your website into a mass credential-harvesting platform.
⚠ Business Impact
Insecure deserialization can result in remote code execution — complete system takeover. Compromised CDN scripts can silently harvest customer payment card data (Magecart-style attacks). Supply chain integrity failures are notoriously difficult to detect and have long dwell times.
✓ How to DefendImplement Subresource Integrity (SRI) for all external scripts and stylesheets. Use digital signatures for all build artifacts and update packages. Avoid deserializing untrusted data; if necessary, use safe libraries with strict type constraints. Verify all CI/CD inputs against known-good checksums.
9. Security Logging and Alerting Failures
Slightly renamed from "Logging and Monitoring" to emphasise alerting as a distinct and critical capability — because excellent logs with no alerting provide essentially zero defensive value. This category persists at #9 and OWASP notes it will always be underrepresented in automated testing data: you cannot reliably scan an application to confirm that its alerts will fire correctly in a real incident. Its inclusion is driven by the community survey — practitioners know from experience just how costly this failure is.
Most businesses significantly underestimate this risk. The global average time to detect a data breach is still measured in months. That window exists almost entirely because security events are either not logged, logs are not centralised, or alerting thresholds are not configured to catch the subtle patterns of an active intrusion. Attackers rely on this visibility gap — modern intrusion techniques are designed to be slow and quiet specifically because detection is poor.
⚠ Business Impact
Extended dwell time during active breaches, allowing attackers to exfiltrate more data and establish deeper persistence. Inability to meet breach notification timelines under GDPR (72 hours) or other regulations. Forensic investigations become impossible without proper audit trails, complicating insurance claims and legal proceedings.
✓ How to Defend
Centralise logs in a tamper-resistant SIEM (Security Information and Event Management) platform. Define logging standards for login attempts, access denials, privilege changes, and validation failures. Configure automated alerting with response runbooks. Run tabletop exercises to test your detection and response capabilities. Ensure log retention meets regulatory requirements in your industry.
10. Mishandling of Exceptional Conditions
The second brand-new category in 2025, with 24 associated CWEs. OWASP's decision to elevate error handling to a dedicated Top 10 category signals a shift in how the industry thinks about failure states. Poor exception handling is not a "code quality" issue — it is a security vulnerability that sophisticated attackers actively probe and exploit.
This category covers a range of failure scenarios: applications that "fail open" — granting access or continuing operations when an error occurs rather than failing safely — are directly exploitable. Verbose error messages that include stack traces, SQL query text, or internal file paths give attackers a free map of your system architecture. Incomplete error recovery leaving shared state in an inconsistent condition can be exploited for data corruption or privilege escalation. Boundary conditions and edge cases that reach unsafe code paths can cause denial-of-service or logic bypass. For businesses processing payments, healthcare data, or legal records, these failure modes carry severe real-world consequences.
⚠ Business Impact
Fail-open conditions can bypass entire authentication and authorisation systems. Information leakage via error messages accelerates attacker reconnaissance, reducing the time and cost of a targeted attack. Service disruption via denial-of-service from unhandled edge cases. Logic errors in financial systems can enable fraud.
✓ How to Defend
Adopt a fail-closed philosophy: default to denying access or aborting when unexpected conditions arise. Sanitise all error messages shown to end users — log full details internally only. Test boundary conditions and edge cases systematically. Conduct chaos engineering exercises to observe failure behaviour. Implement structured exception handling frameworks across all codebases.
Why This Matters to Your Business in 2026
The OWASP Top 10 is not an academic exercise. Each category on this list has a direct line to business consequences that boards, executives, and legal teams care about.
💸 Financial Exposure
The average cost of a data breach now exceeds $4.8 million. Regulatory fines under GDPR can reach 4% of global annual turnover. Ransomware demands continue to escalate across all sectors.
⚖️ Regulatory Compliance
GDPR, HIPAA, PCI-DSS, and ISO 27001 all mandate controls that directly address OWASP risks. A failure against this list is often a compliance failure with legal consequences.
🏆 Competitive Trust
Security posture is increasingly part of enterprise vendor due diligence. A breach — or even a disclosed vulnerability — can cost you customers, partnerships, and procurement deals.
🔗 Supply Chain Liability
With A03 now in the Top 10, the legal and business liability of software supply chain failures is in focus. Third-party risk management is no longer optional for any serious organisation.